Being first is usually a badge of honor, but not in this case. The United States remains the top target for ransomware groups, absorbing 55% of all attacks in 2025, followed by Canada.
Healthcare is also under siege. It now ranks fourth in ransomware attacks, with 697 reported breaches (of 500 or more records) in 2025. Even more concerning, most organizations fail to explain how those breaches actually occurred.
Recent incidents have sparked some positive momentum. Hospitals and medical practices are strengthening their security posture. As a result, the U.S. healthcare cybersecurity market is projected to reach USD 41.24 billion by 2035.
Yet, while practices focus on well-known threats like phishing, smishing, and ransomware, there are blind spots that hackers exploit precisely because they’re overlooked. These weak entry points are easy to target, hard to detect, and devastating when breached. Let’s walk through eight critical blind spots every healthcare practice should address before it's too late.
The Internet of Medical Things (IoMT) refers to medical or clinical devices such as imaging systems, patient monitors, surgical devices, and information systems connected to a network. In a recent report by Claroty, an alarming 99% of hospitals and large healthcare organizations are operating IoMT devices with known exploited vulnerabilities (KEVs).
Many IoMT devices are poorly secured when connected to the internet, making them attractive entry points for ransomware campaigns. Once an IoMT device is compromised, attackers can often move laterally into more critical systems such as electronic health records (EHRs) and administrative platforms. They can even disrupt patient care, for example, by tampering with dosage controllers or delaying access to diagnostic tools.
Managing IoMT risks requires more than just listing devices. A clear, step-by-step strategy helps practices stay secure:
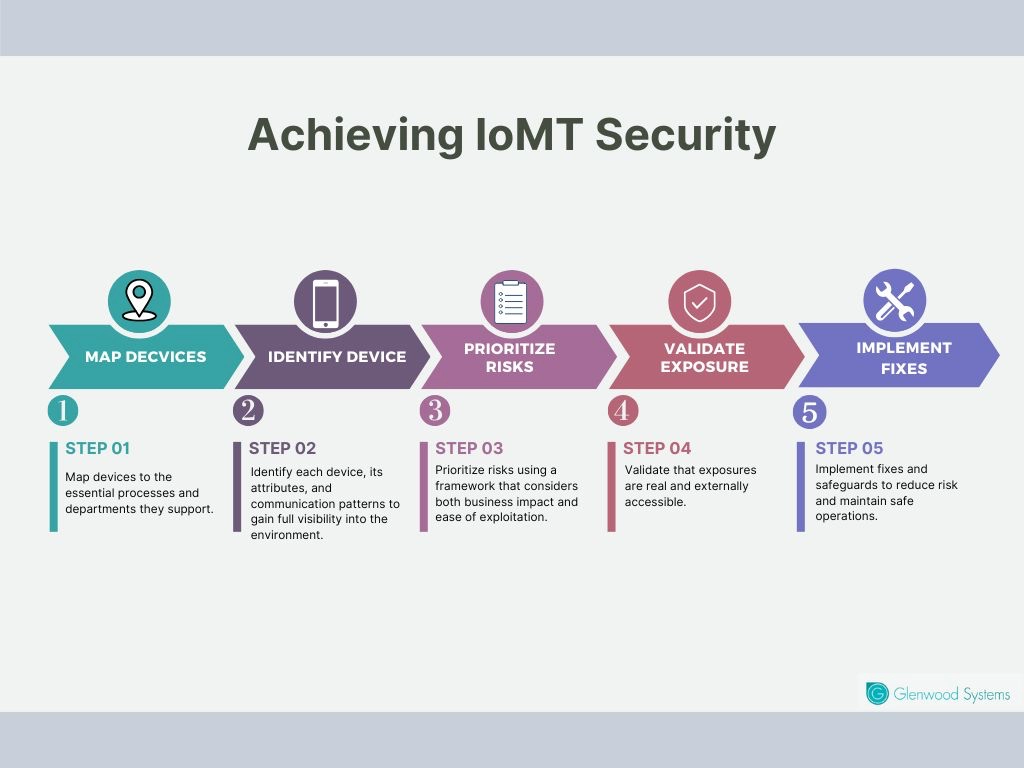
Managing IoMT Risks
This might sound basic, but you’d be surprised how often devices or systems come with credentials (usernames & passwords) embedded in the code, or with default logins that are never changed. Sometimes these credentials can’t even be modified by the user. For example, many infusion pumps and networked printers arrive with hardcoded ‘admin/admin’ logins that remain active unless deliberately disabled. Attackers know to scan for these weak entry points and try them first.
Hardcoded credentials hand attackers instant privileged access, eliminating the need to break in or steal credentials. Implement these best practices to prevent risks of hardcoded credentials:
You may have solid internal security, but what about your vendors, your device manufacturers, your billing partners, or cloud/backup providers? If they have weak security, attackers will often use them as stepping stones.
This isn’t a hypothetical risk. The trend of supply chain attacks is accelerating, largely because a single compromised vendor can gain access to hundreds of interconnected organizations. In 2025, the ITRC recorded 133 such incidents that impacted 1252 companies and exposed the personal data of more than 98 million people.
Every partner should meet the same security standards you enforce internally. To minimize third-party risks, you should:
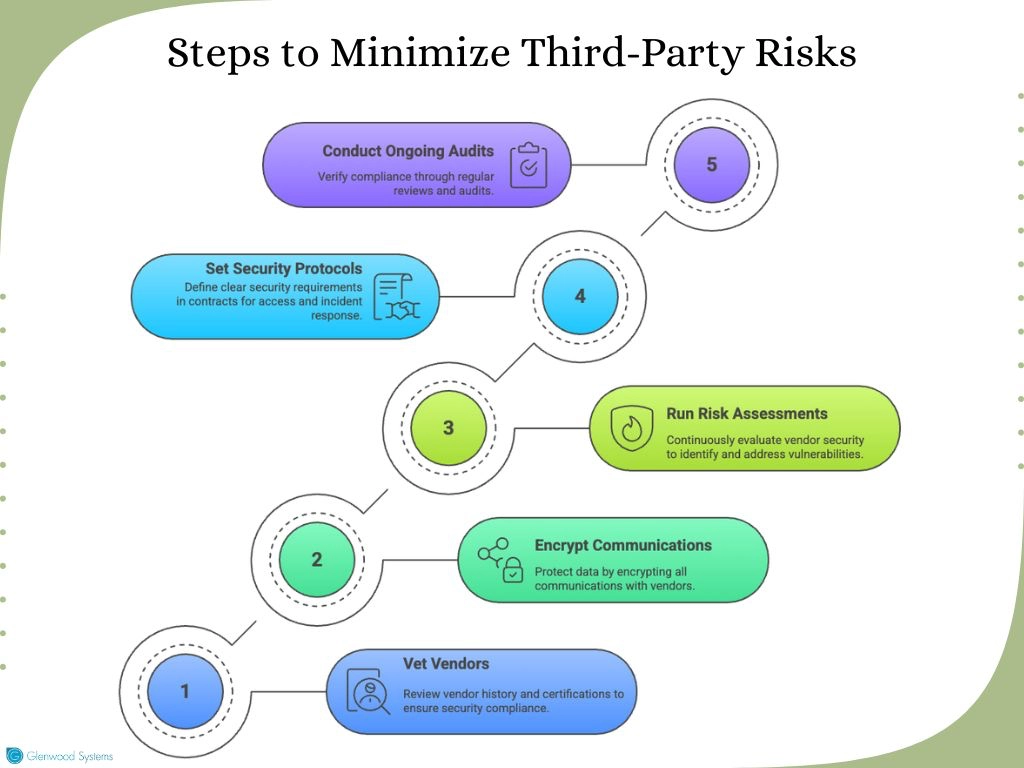
Mitigating Third-Party Risks
Effective vendor management practices seal gaps that hackers increasingly target.
Shadow IT refers to software or services used by staff without the knowledge or approval of the central IT/security team. Bring-Your-Own-Device (BYOD) practices are a classic component. A nurse using a personal tablet, or staff members using consumer messaging apps to share patient info, are some examples.
A well-known case highlighting shadow IT risks occurred during the Okta breach in late 2023. An employee synced a personal Google account to a company laptop, exposing credentials tied to Okta’s customer support system. Attackers exploited this lapse to access sensitive support files and session tokens, ultimately impacting 134 customers.
Shadow IT creates easy entry points for hackers because:
Some leaders tolerate shadow IT because it saves time, boosts agility, and allows staff to innovate without waiting for IT approval. While this flexibility can be valuable, it often comes at the expense of security.
Nevertheless, modern tools can now scan across private clouds, data centers, and public clouds to identify unauthorized assets, giving IT teams clearer visibility into where shadow IT resides. CIOs and IT managers should also establish clear policies, allow limited use of shadow IT for non-PHI workloads under strict time limits, and involve expert oversight when patient health information is at stake. This approach balances innovation with the safeguards healthcare demands.
Digital certificates (for TLS/SSL, etc.) are essential for securing communications, especially for web portals, internal intranet, and device-to-device communications. Despite their importance, many organizations still manage certificates manually, tracking expiration dates in spreadsheets or relying on staff to remember renewals.
Expired certificates can disrupt services, causing web portals or internal interfaces to stop functioning. They may also trigger security warnings that erode user trust. In addition, misconfigured or outdated certificates can expose systems to man-in-the-middle attacks and other interception risks.
Manual tracking of digital certificates is risky and error-prone, especially in complex healthcare environments with numerous servers, devices, and applications. Automating certificate management eliminates the risks of manual tracking by ensuring certificates are renewed, replaced, and monitored without relying on staff. It enables proactive renewals to prevent service outages, consistent deployment across systems and devices, real-time visibility into all certificates, and streamlines compliance with audits and regulations.
Mobile devices, including laptops, tablets, and smartphones, are ubiquitous in healthcare settings, facilitating tasks like charting, diagnostic analysis, and telehealth consultations. However, if these endpoints are inadequately secured, they become prime targets for cyberattacks.
Common risks that make unprotected devices prime targets:
Enforce comprehensive security measures, including antivirus software and firewalls, and deploy Endpoint Detection & Response (EDR) tools to monitor and respond to suspicious activity in real-time. Secure cloud or encrypted solutions should be favoured over local storage, and devices should have remote wipe capabilities to protect information in the event of loss or theft. Implementing these measures helps healthcare organizations reduce risks, safeguard patient data, and maintain trust.
Phishing attacks are not new, but AI has made them far more sophisticated and scalable. Cybercriminals can now craft highly personalized emails, mimic internal communications, tailor subject lines to social media activity, and in some cases even use deepfake audio for “voice phishing.”
The weaponization of AI in phishing is unprecedented. Deep Strike reports a 1,265% increase in phishing emails since the advent of generative AI. Likewise, another report by KnowBe4 found that AI-generated content now appears in roughly 82.6% of phishing emails, making these attacks increasingly difficult to distinguish from legitimate communications.
Given this heightened risk, practices must adopt proactive defenses that equip staff and systems to detect and respond effectively. Action steps to strengthen defenses include:
Employee negligence remains one of the primary drivers of healthcare data breaches. A 2024 survey revealed that 68% of incidents were tied to human error. Seemingly small lapses, such as clicking on a phishing link, sending sensitive information to the wrong recipient, or failing to log out of systems, can quickly escalate into serious security exposures.
Cybersecurity training in healthcare often emphasizes clinicians, but non-clinical staff (admin, billing, reception) are frequently overlooked. Yet these individuals regularly handle protected health information (PHI), manage system credentials, and interact with vendors, making them equally critical to security.
Seal knowledge gaps with robust employee training:
Investing in staff education mitigates insider threats and empowers every employee to play their role in protecting sensitive information.
Security underpins everything we do at Glenwood Systems. By adhering to industry standards and regulations, we ensure delivery of the highest quality of care. Our robust cybersecurity framework safeguards sensitive information, strengthens operational reliability, and ensures that healthcare services remain safe, secure, and resilient.
Together, let's achieve excellence in care delivery while upholding the highest standards of security and trust.
Schedule a Free Consultation!
